When businesses grow, managing who can access what becomes serious business. One wrong access permission can lead to data leaks, compliance penalties, or financial damage.
In fact, IBM’s Cost of a Data Breach Report 2024 found that the average global data breach cost reached $4.88 million, the highest ever recorded. These numbers necessitate the requirement of having strong access control in place.
Verizon’s Data Breach Investigations Report consistently shows that over 74% of breaches involve stolen credentials or misuse of access privileges. These numbers highlight why choosing the right access control model matters.
This guide explains RBAC vs. CBAC in simple terms, compares their features, and helps you decide which model works best for your organization.
What Is Role-Based Access Control?
Role-Based Access Control, often shortened to RBAC, is a system where access permissions are assigned based on a user’s role within an organization.
In the context of access control, RBAC is the traditional and widely used approach. Instead of giving permissions to each user, administrators create roles such as HR Manager, IT Administrator, Sales Executive, and Finance Officer.
Each role has predefined permissions. When a user joins the organization, they are assigned a role. That role determines their access rights.
Key Features of RBAC
- Access is based on job function
- Permissions are grouped by role
- Easy to manage in structured organizations
- Supports the principle of least privilege
In the RBAC vs. CBAC debate, RBAC is known for its simplicity and scalability in stable environments.
What Is Context-Based Access Control?
Context-Based Access Control (CBAC) extends access decisions by considering context. Instead of considering only a user’s role, it evaluates the context of the access request.
In context-based access control vs role-based access control, CBAC considers multiple real-time factors such as:
- User location
- Device type
- Time of access
- Network security level
- Risk score
For example, an employee may normally have access to financial data. But if they attempt to log in from an unknown country at midnight using an unrecognized device, CBAC can deny or restrict access.
In the ongoing comparison of RBAC vs. CBAC, CBAC is considered more dynamic and intelligent.
RBAC vs. CBAC: Key Differences Explained
To properly understand RBAC vs. CBAC, the table below explains the core differences between context-based access control vs role-based access control options so businesses can make a smart decision:
| Basis of Comparison | Role-Based Access Control (RBAC) | Context-Based Access Control (CBAC) |
| Definition | Access is granted based on a user’s predefined role within the organization. | Access is granted based on real-time context, including location, device, time, and risk level. |
| Access Decision Factor | User’s job role | Role + contextual factors like IP address, device health, and login time |
| Dynamic Capability | Static. Permissions remain fixed unless manually changed. | Dynamic. Access decisions change based on situational conditions. |
| Security Level | Strong baseline security using the least privilege principle. | Higher security due to adaptive and risk-aware decision-making. |
| Flexibility | Less flexible once roles are defined. | Highly flexible and adaptive to changing environments. |
| Ease of Implementation | Easier to implement and manage. | More complex to implement and requires monitoring systems. |
| Best For | Organizations with stable roles and a structured hierarchy. | Cloud environments, remote workforce, and Zero Trust security models. |
| Risk Handling | Does not automatically detect unusual access behavior. | Can restrict or block access if suspicious behavior is detected. |
| Compliance Support | Helps meet compliance requirements with structured permission control. | Enhances compliance with real-time monitoring and risk evaluation. |
| Integration with Modern Security | Works well within traditional IT and structured AI Data Governance Framework setups. | Works well with Zero Trust, data tokenisation, and Agentic data classification models. |
| Example Scenario | A Finance Manager always has access to payroll data based on their role. | The Finance Manager can access payroll data only if logging in from a trusted device and an approved location. |
Can RBAC and CBAC Work Together?
Yes. In fact, many organizations use a hybrid approach.
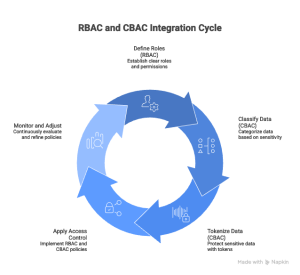
In modern cybersecurity, the RBAC vs. CBAC discussion often leads to integration rather than replacement.
A layered strategy looks like this:
- RBAC assigns baseline permissions
- CBAC evaluates real-time conditions
- Agentic data classification identifies data sensitivity
- Data tokenisation protects high-risk information
- AI Data Governance Framework ensures oversight
The collaboration can provide both structure and intelligence.
Implementation Challenges
When comparing RBAC and CBAC, it is important to understand that both models have practical challenges. The correct choice for any business essentially depends not only on security needs but also on factors like resources, complexity, and long-term management.
Challenges of Role-Based Access Control (RBAC)
-
Role Explosion
As organizations grow, the number of roles can increase quickly. Too many roles make administration and audits difficult.
-
Limited Flexibility
In the context-based access control vs role-based access control debate, RBAC is much more static. It does not evaluate real-time factors such as device risk or unusual login locations.
-
Ongoing Maintenance
Role definitions must be reviewed regularly. If not updated, users may retain unnecessary access, increasing security risk.
Challenges of Context-Based Access Control (CBAC)
- Higher Complexity
CBAC requires risk engines, real-time monitoring, and advanced policy management systems. Thus, implementation is much more technical than in traditional RBAC setups.
- Increased Cost
When businesses are looking to deploy AI-driven monitoring and contextual analysis tools, they require investment in infrastructure and expertise.
- Policy Management Issues
Contextual rules must be carefully configured. When the policies are strict, it can disrupt user productivity, while weak policies can also reduce security effectiveness.
Governance Requirements
Both models need strong oversight. RBAC depends on clear role definitions within an AI Data Governance Framework. CBAC works best when supported by Agentic data classification and data tokenisation to protect sensitive information.
Which One Should You Choose?
Deciding on context-based access control vs role-based access control depends on your business needs.
- Choose RBAC if: You have a physical office, most employees work on-site, and your data doesn’t change frequently. It is a solid, reliable choice for standard business operations.
- Choose CBAC if: You have a remote team, handle highly sensitive customer data, or want the highest level of security.
In many cases, the best answer to RBAC vs. CBAC is “both.” Modern security experts suggest using RBAC to define the baseline of what a person can do, and using CBAC to determine whether the current situation allows them to do it now.
Future of Access Control
The future clearly leans toward intelligent systems. As AI and machine learning evolve, contextual analysis will become more accurate.
However, RBAC will not disappear. It remains a strong foundation for structured access management.
In the evolving discussion of RBAC vs. CBAC, the trend is toward the increasing adoption of contextual and risk-based models layered on top of traditional role-based systems.
Conclusion
Understanding the differences in RBAC vs. CBAC is important for anyone who wants to protect their business. RBAC offers a clear, structured way to manage people based on their jobs. CBAC offers a smart, situational approach to data protection based on a user’s surroundings.
Whether you prefer the simplicity of role-based access control or the high-tech protection of context-based access control, the goal is the same: keeping your information safe. By combining these methods with tools such as data tokenisation and clear governance, you can build a digital fortress to protect your company’s future.
Frequently Asked Questions
What is the main difference between RBAC and CBAC?
The main difference between RBAC and CBAC is how access decisions are made. RBAC grants access based on predefined job roles; on the other hand, CBAC evaluates real-time contextual factors, such as location, device, and risk level, before granting access.
Can RBAC and CBAC be used together?
Yes. Many organizations combine both models. In the RBAC vs CBAC approach, RBAC provides baseline permissions, while CBAC applies real-time risk evaluation to strengthen security.
How does CBAC improve cybersecurity?
CBAC is known to improve cybersecurity by analyzing contextual signals such as login time, device health, and user location. In the context of access control, CBAC helps prevent unauthorized access even in the case that credentials are stolen.
How does RBAC vs. CBAC impact remote work security?
In remote work environments, RBAC vs. CBAC comparisons often favor CBAC. It can detect risky login attempts from unknown locations or devices and apply additional security checks.