In the ever-evolving landscape of security and privacy, de-identification of sensitive data stands paramount. Both Protecto and the open-source alternative, Presidio, address this imperative need. On first impression, both might appear to address identical needs, but for enterprise-grade requirements, these differences are substantial and can’t be overlooked.
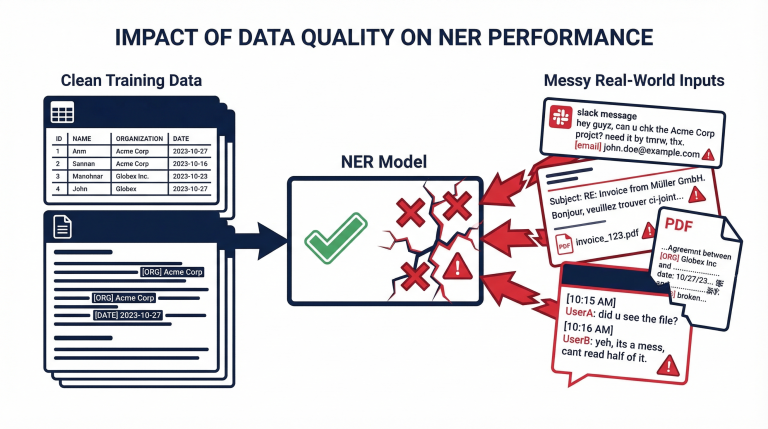
Accuracy and Scope of Sensitive Data:
Protecto uses multiple models to understand context and locate sensitive data, which enhances accuracy and effectiveness in masking sensitive data. We started with Spacy, which Presidio uses, but we have moved to an ensemble of various models (NER, Algo, Regex, Heuristic) to increase accuracy.
Meet Microsoft Presidio Alternatives: Protecto’s Cutting-Edge Personal Data Identification
“Analyzable” Masking:
Protecto offers customizable tokenization options that allow you to preserve the format, type, and length of data in the masked data. For example, if you decide to preserve the original format, a phone number will be masked with delimiters like (555) 787-8999. This allows you to conduct analyses based on specific elements, such as the area code. Similarly, we can configure the masked data to exclusively consist of numbers or alphanumeric characters, providing flexibility in data masking options.
Intelligent Tokenization: Protecto’s Technical Edge in Data Privacy
“LLM Understandable” Masking:
Through fine-tuning, we give the right instructions so that LLMs fully understand the data masked by Protecto. However, if you use other solutions for masking sensitive data, LLMs understandability of the input/prompts drops and the effectiveness of the results will suffer.
Strong Security:
Protecto’s true random number-based tokenization is designed to be more secure. Protecto’s tokens are difficult to reverse engineer. Compared to Presidio, the risk of breach associated with transmitting encryption keys is high. You have to implement key management, etc., to make it more secure.
Protecto’s Edge In Cybersecurity: Random Tokenization
Blast Radius of an incident:
Protecto generates tokens without a discernible pattern, which adds an extra layer of security. Even if one token is compromised, it doesn’t compromise the security of other tokens, as there is no predictable pattern to exploit. On the other hand, in the case of using encryption, if a key is compromised, all the masked data using the key will be at risk.
Purging for Compliance:
Protecto provides a convenient way to purge personal data for compliance purposes. Eventually, when you need to purge a specific PII for data retention or DSAR requirements, a single call to Protecto will efficiently remove the mapping. In the case of encryption, you must search for the encrypted data across the entire data source to find and replace it.
Additionally, Protecto is specifically engineered for enterprise-grade demands, ensuring robust support and unwavering commitment through our stringent Service Level Agreements (SLA) and easy integration.
Strong SLA Commitments:
We understand the critical nature of data de-identification. Our Service Level Agreements (SLA) underscore our commitment to upholding the highest standards of service, guaranteeing not just uptime but also a consistently high level of performance.
Easy Integration:
We pride ourselves on the ease with which organizations can integrate Protecto into their existing systems. A straightforward API and comprehensive documentation mean that you can get started with Protecto quickly and with minimal disruption.
Protecto brings to the table advanced features and guarantees that cater to enterprises with uncompromising demands. When it comes to ensuring data security and privacy without compromising on usability and efficiency, Protecto clearly stands out.