AI agents are no longer experimental. They query your databases, call your APIs, read customer records, and make decisions all without a human in the loop. That capability is powerful. It is also a significant security risk if you have not answered one foundational question: who controls what your AI agents can access?
The answer lies in role-based access control for ai, and getting it right is now one of the most critical challenges in enterprise AI security.
What Is Role-Based Access Control (RBAC)?
Every organization has sensitive data, and not everyone should see all of it. Role-based access control (RBAC) is how enterprises manage that boundary. Instead of setting permissions per person, RBAC groups users into roles and defines what each role can access.
For example: A finance analyst can view revenue reports. A customer support rep cannot. An IT admin can modify system configurations. A junior employee cannot. This is RBAC access control in its simplest form, structured, scalable, and auditable.
RBAC software sits at the heart of most enterprise security stacks, often connected to identity systems like Active Directory (AD) to map users to roles automatically. When someone logs in, their role determines what they see. It’s automatic, consistent, and easy to audit for compliance. RBAC is the backbone of enterprise RBAC security frameworks. It enforces least-privilege access, simplifies policy management, and creates the audit trails required by SOC 2, HIPAA, GDPR, and other compliance standards.
How RBAC Is Applied in AI Systems
Deploying RBAC in AI systems follows the same logic as in traditional IT, but with one major shift: AI agents must be treated as first-class principals, not invisible background processes.
Every AI agent in your stack should carry an explicit identity, be assigned one or more roles, and operate strictly within the permissions those roles allow. This applies whether the agent is a customer support bot, an internal research assistant, or an autonomous multi-step workflow.
- Which data sources an agent can query, including databases, document stores, and third-party APIs
- Which tools an agent is allowed to invoke web search, code execution, CRM lookups, email drafting
- The scope of actions the agent can take read-only vs. read-write vs. full administrative access
- What user context the agent is permitted to inherit during a delegated session
For AI research tools with role-based access and security controls, this means researchers can deploy agents that surface insights from approved datasets without those agents ever touching restricted data they have no business seeing. Policy-based access control for AI takes this further, layering dynamic rules on top of static roles to handle conditional access logic in real time.
The Challenges of RBAC in AI Systems
RBAC software was originally built for predictable, deterministic systems. AI agents are neither. They plan, reason, and act dynamically which breaks several assumptions that traditional RBAC access control was built on.
- Agents operate at machine speed. A human employee requests access consciously. An AI agent makes hundreds of access decisions per minute, automatically. Without RBAC permissions enforced at every decision point, a single misconfiguration can result in large-scale unauthorized data exposure before anyone notices.
- Inherited context creates privilege escalation. When an AI agent runs on behalf of a user, it often inherits that user’s session permissions. If the user holds elevated privileges, the agent silently gains them too far beyond what the task requires. True RBAC for ai agents requires scoping permissions to the task, not the triggering user’s full access profile.
- Multi-agent pipelines blur accountability. Modern agentic systems chain agents together one agent plans, another executes, a third summarizes. As context flows between agents, it becomes unclear which role governs which action. Without explicit AI agent access policies at every handoff point, permissions propagate unchecked through the entire pipeline.
- Tool use is dynamic and hard to pre-authorize. AI agents decide which tools to call at inference time. Static role definitions cannot anticipate every tool an agent might invoke in a complex workflow. This demands a shift from pre-approved tool lists to real-time policy evaluation at the moment of action.
- Auditability is largely absent. Traditional RBAC security frameworks produce access logs for every human action. Most AI frameworks today produce no equivalent. Without logs showing which agent accessed which resource under which role, organizations cannot satisfy compliance audits or investigate incidents.
How Protecto Enforces RBAC for AI Agents
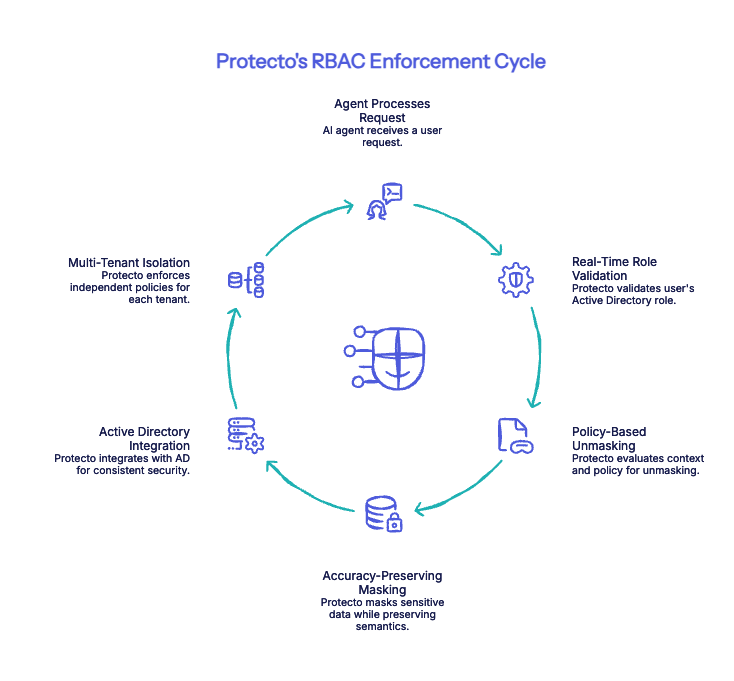
Protecto is built specifically for this problem. It acts as the access control and policy enforcement layer between your AI agents and your sensitive data integrated with your existing enterprise identity stack, enforcing permissions in real time, and doing it without degrading agent performance.
- Real-Time Role Validation: When an agent processes a request, Protecto checks the user’s Active Directory role and determines what data can be exposed automatically. A support agent sees masked identifiers. A senior analyst sees the full record. No manual configuration. No rule-writing per agent.
- Policy-Based Unmasking: Protecto goes beyond static RBAC by evaluating context alongside role. It considers who is asking, what the agent is doing, and what the data contains before deciding whether unmasking is permitted. This is policy-based access control for AI dynamic, not just declarative.
- Accuracy-Preserving Masking: Data masking can sometimes affect how well an LLM reasons over restricted content. Protecto is designed to preserve the semantic structure that models need to stay accurate masking sensitive fields without degrading the agent’s ability to do its job. Agents remain effective even when working with partially restricted data.
- Active Directory Integration: Protecto connects directly to enterprise AD systems, so RBAC security in AI is grounded in the same identity layer governing your non-AI systems. No duplicate policy management. No separate access stack to maintain.
- Multi-Tenant Isolation: For platforms serving multiple enterprise customers, Protecto enforces independent RBAC access control policies per tenant, and also centrally managed, cleanly separated.
The Access Control Gap You Cannot Afford to Ignore
The organizations winning with AI are not the ones that deploy the most agents, they are the ones that deploy agents they can trust. Trust requires knowing, at every moment, what your AI systems can and cannot do. Role-based access control for AI is the foundation of that trust. Without it, every AI agent you deploy is a potential compliance liability, a data breach waiting to happen, and an audit failure in progress.
With Protecto’s purpose-built RBAC for AI agents, you can move fast and stay secure by giving your AI the access it needs, and nothing more.
Take control of your AI access policies See How Protecto Secures AI Agents →